Reviews of Notes Taken From Users in Cyber Security
Cybersecurity is the protection of internet-connected systems such equally hardware, software and data from cyberthreats. The practice is used by individuals and enterprises to protect against unauthorized access to data centers and other computerized systems.
A strong cybersecurity strategy tin provide a expert security posture against malicious attacks designed to access, alter, delete, destroy or extort an organization's or user's systems and sensitive data. Cybersecurity is as well instrumental in preventing attacks that aim to disable or disrupt a system'southward or device's operations.
Why is cybersecurity important?
With an increasing number of users, devices and programs in the modernistic enterprise, combined with the increased deluge of information -- much of which is sensitive or confidential -- the importance of cybersecurity continues to grow. The growing volume and sophistication of cyber attackers and attack techniques chemical compound the problem fifty-fifty further.
What are the elements of cybersecurity and how does information technology work?
The cybersecurity field can exist cleaved down into several different sections, the coordination of which inside the arrangement is crucial to the success of a cybersecurity program. These sections include the following:
- Application security
- Information or data security
- Network security
- Disaster recovery/business concern continuity planning
- Operational security
- Cloud security
- Disquisitional infrastructure security
- Physical security
- End-user educational activity
Maintaining cybersecurity in a constantly evolving threat landscape is a challenge for all organizations. Traditional reactive approaches, in which resources were put toward protecting systems against the biggest known threats, while lesser known threats were undefended, is no longer a sufficient tactic. To keep up with changing security risks, a more than proactive and adaptive approach is necessary. Several central cybersecurity advisory organizations offering guidance. For example, the National Institute of Standards and Technology (NIST) recommends adopting continuous monitoring and real-time assessments as part of a risk assessment framework to defend against known and unknown threats.
What are the benefits of cybersecurity?
The benefits of implementing and maintaining cybersecurity practices include:
- Business protection against cyberattacks and information breaches.
- Protection for data and networks.
- Prevention of unauthorized user admission.
- Improved recovery time after a breach.
- Protection for end users and endpoint devices.
- Regulatory compliance.
- Business concern continuity.
- Improved confidence in the company's reputation and trust for developers, partners, customers, stakeholders and employees.
What are the different types of cybersecurity threats?
The procedure of keeping upwardly with new technologies, security trends and threat intelligence is a challenging task. It is necessary in order to protect information and other avails from cyberthreats, which have many forms. Types of cyberthreats include:
- Malware is a grade of malicious software in which any file or program tin be used to harm a computer user. This includes worms, viruses, Trojans and spyware.
- Ransomware is another type of malware. Information technology involves an assailant locking the victim's computer system files -- typically through encryption -- and demanding a payment to decrypt and unlock them.
- Social engineering is an attack that relies on homo interaction to trick users into breaking security procedures to gain sensitive data that is typically protected.
- Phishing is a class of social engineering where fraudulent email or text messages that resemble those from reputable or known sources are sent. Often random attacks, the intent of these letters is to steal sensitive data, such as credit card or login information.
- Spear phishing is a blazon of phishing attack that has an intended target user, organization or concern.
- Insider threats are security breaches or losses caused by humans -- for instance, employees, contractors or customers. Insider threats tin can be malicious or negligent in nature.
- Distributed denial-of-service ( DDoS ) attacks are those in which multiple systems disrupt the traffic of a targeted system, such as a server, website or other network resource. Past flooding the target with messages, connection requests or packets, the attackers can boring the system or crash it, preventing legitimate traffic from using it.
- Advanced persistent threats ( APTs ) are prolonged targeted attacks in which an attacker infiltrates a network and remains undetected for long periods of time with the aim to steal data.
- Homo-in-the-middle ( MitM ) attacks are eavesdropping attacks that involve an assaulter intercepting and relaying messages between two parties who believe they are communicating with each other.
Other mutual attacks include botnets, drive-by-download attacks, exploit kits, malvertising, vishing, credential stuffing attacks, cross-site scripting (XSS) attacks, SQL injection attacks, business email compromise (BEC) and zero-day exploits.

What are the height cybersecurity challenges?
Cybersecurity is continually challenged by hackers, data loss, privacy, risk direction and irresolute cybersecurity strategies. The number of cyberattacks is not expected to decrease in the well-nigh futurity. Moreover, increased entry points for attacks, such as with the inflow of the internet of things (IoT), increase the demand to secure networks and devices.
One of the most problematic elements of cybersecurity is the evolving nature of security risks. Every bit new technologies emerge, and every bit technology is used in new or unlike means, new assail avenues are developed. Keeping upwards with these frequent changes and advances in attacks, besides as updating practices to protect against them, can be challenging. Issues include ensuring all elements of cybersecurity are continually updated to protect confronting potential vulnerabilities. This can be especially difficult for smaller organizations without the staff or in-house resources.
Additionally, organizations can gather a lot of potential data on individuals who use one or more of their services. With more data being nerveless, the likelihood of a cybercriminal who wants to steal personally identifiable information (PII) is some other concern. For example, an system that stores PII in the cloud may exist subject to a ransomware attack. Organizations should do what they can to prevent a cloud alienation.
Cybersecurity programs should likewise address terminate-user education, as employees may accidently bring viruses into the workplace on their laptops or mobile devices. Regular security awareness training will assist employees do their office in keeping their visitor safe from cyberthreats.
Some other challenge to cybersecurity includes a shortage of qualified cybersecurity personnel. As the corporeality of data nerveless and used by businesses grows, the need for cybersecurity staff to clarify, manage and answer to incidents also increases. (ISC)2 estimated the workplace gap between needed cybersecurity jobs and security professionals at three.one million.
How is automation used in cybersecurity?
Automation has go an integral component to keep companies protected from the growing number and sophistication of cyberthreats. Using bogus intelligence (AI) and auto learning in areas with high-volume data streams can help meliorate cybersecurity in three main categories:
- Threat detection. AI platforms tin analyze data and recognize known threats, as well as predict novel threats.
- Threat response. AI platforms also create and automatically enact security protections.
- Homo augmentation. Security pros are often overloaded with alerts and repetitive tasks. AI tin assistance eliminate alert fatigue past automatically triaging low-gamble alarms and automating big data assay and other repetitive tasks, freeing humans for more than sophisticated tasks.
Other benefits of automation in cybersecurity include attack classification, malware classification, traffic analysis, compliance analysis and more.
Cybersecurity vendors and tools
Vendors in the cybersecurity field typically offer a multifariousness of security products and services. Common security tools and systems include:
- Identity and access management (IAM)
- Firewalls
- Endpoint protection
- Antimalware
- Intrusion prevention/detection systems (IPS/IDS)
- Data loss prevention (DLP)
- Endpoint detection and response
- Security information and outcome management (SIEM)
- Encryption tools
- Vulnerability scanners
- Virtual private networks (VPNs)
- Cloud workload protection platform (CWPP)
- Cloud admission security broker (CASB)
Well-known cybersecurity vendors include Check Signal, Cisco, Code42, CrowdStrike, FireEye, Fortinet, IBM, Imperva, KnowBe4, McAfee, Microsoft, Palo Alto Networks, Rapid7, Splunk, Symantec, Trend Micro and Trustwave.
What are the career opportunities in cybersecurity?
As the cyberthreat landscape continues to grow and new threats emerge -- such every bit IoT threats -- individuals are needed with cybersecurity awareness and hardware and software skills.
Information technology professionals and other computer specialists are needed in security roles, such as:
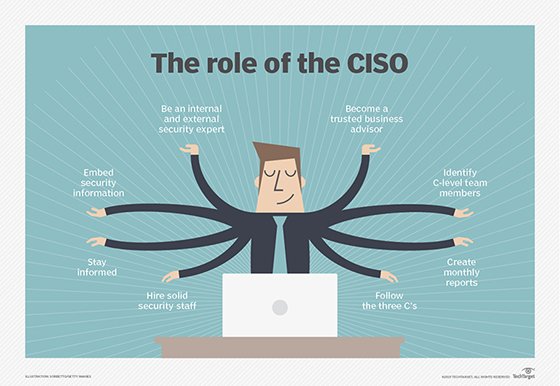
- Chief data security officer ( CISO ) is the private who implements the security program beyond the system and oversees the It security section'southward operations.
- Chief security office ( CSO ) is the executive responsible for the concrete and/or cybersecurity of a company.
- Security engineers protect company assets from threats with a focus on quality control within the Information technology infrastructure.
- Security architects are responsible for planning, analyzing, designing, testing, maintaining and supporting an enterprise's critical infrastructure.
- Security analysts have several responsibilities that include planning security measures and controls, protecting digital files, and conducting both internal and external security audits.
- Penetration testers are ethical hackers who exam the security of systems, networks and applications, seeking vulnerabilities that could be exploited by malicious actors.
- Threat hunters are threat analysts who aim to uncover vulnerabilities and attacks and mitigate them before they compromise a business.
Other cybersecurity careers include security consultants, data protection officer, cloud security architects, security operations manager (SOC) managers and analysts, security investigators, cryptographers and security administrators.
This was terminal updated in Baronial 2021
Proceed Reading Nearly What is cybersecurity?
- 10 all-time cybersecurity online courses for 2021
- Height ten cybersecurity certifications to boost your career in 2021
- How to gear up the top 5 cybersecurity vulnerabilities
- How can you ensure cybersecurity while employees work remote?
- What coding skills do cybersecurity professionals need?
Dig Deeper on Security operations and management
Source: https://www.techtarget.com/searchsecurity/definition/cybersecurity
0 Response to "Reviews of Notes Taken From Users in Cyber Security"
Post a Comment